Estimated Reading & Lab Time: 20 minutes
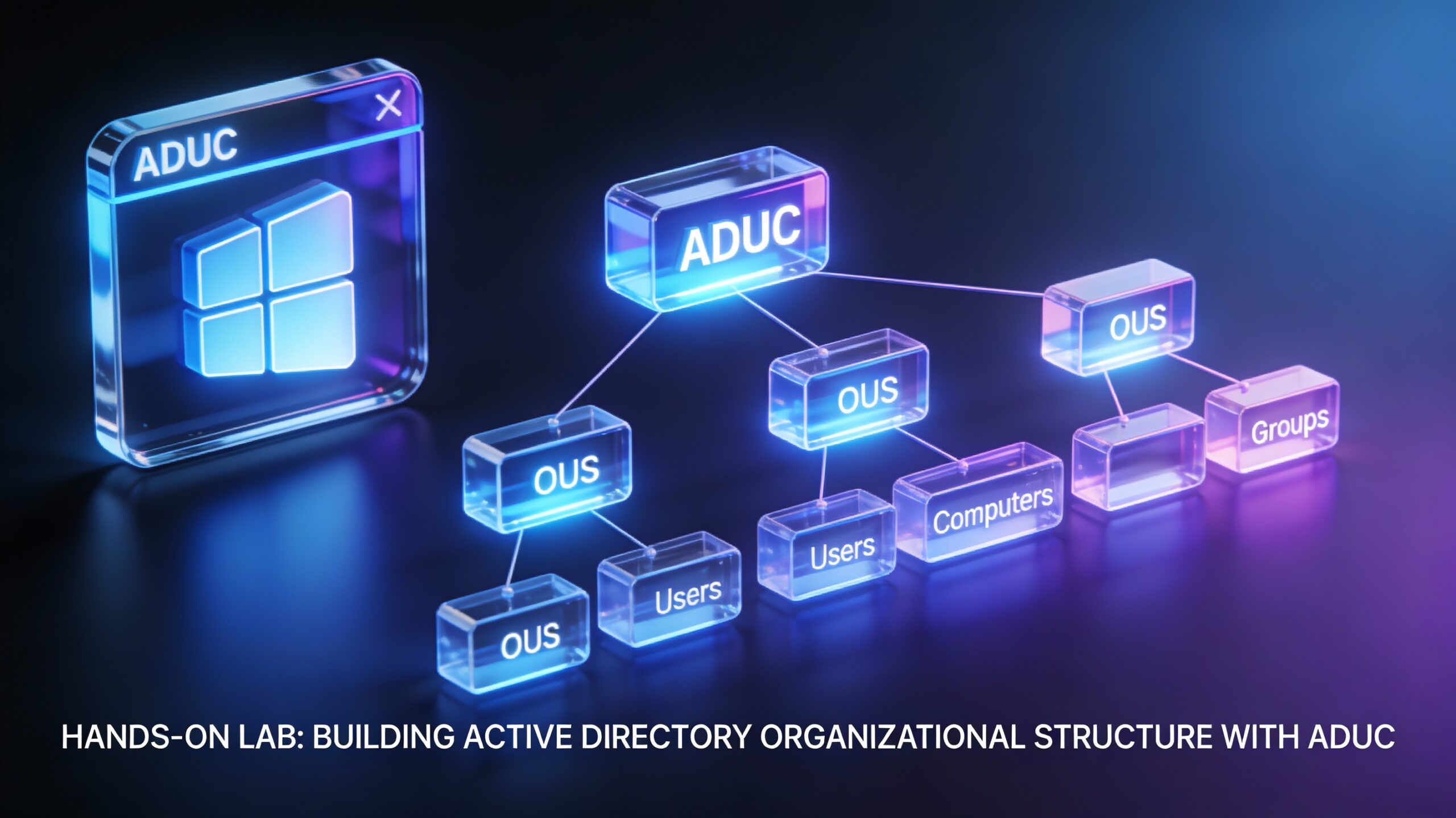
Struggling to organize users across departments in Active Directory? This hands-on lab walks you through creating a realistic OU structure with users and groups using ADUC – covering 80% of daily AD admin tasks. You’ll learn What You’ll Learn: Build 3-level OU hierarchy (Departments → Teams → Sub-teams), create 25+ users across 4 departments, security groups, PowerShell automation, and verification commands.
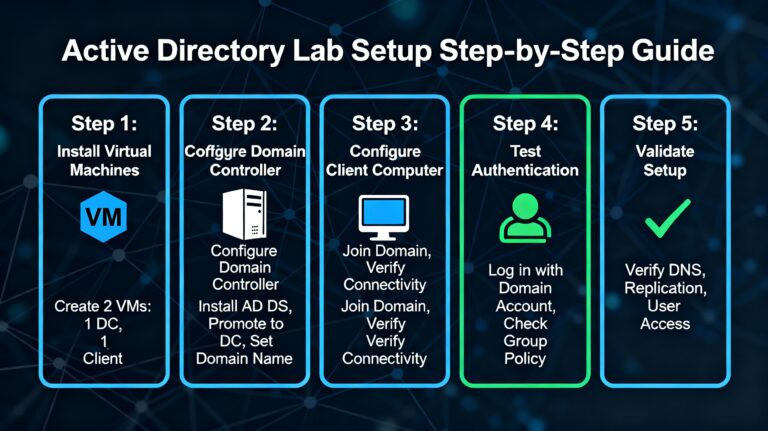
LAB PREREQUISITES
- Windows Server 2022/2019/2016 with Active Directory Domain Services (AD DS) installed and promoted as Domain Controller
- Logged in as Domain Administrator (e.g., CORP\Administrator)
- Active Directory Users and Computers (ADUC) available: Server Manager → Tools → Active Directory Users and Computers
- PowerShell with ActiveDirectory module:
Import-Module ActiveDirectory - Lab Environment: Single-domain setup (e.g., corp.local) – no production changes!
⚠️ Warning: Uncheck “Protect from accidental deletion” on OUs for easy lab cleanup. Re-enable in production. Backup NTDS.dit (C:\Windows\NTDS\ntds.dit) before starting.2
STEP 1: CREATE DEPARTMENTAL OU STRUCTURE
Mirror a real SMB with IT, Finance, HR, Marketing departments and sub-teams.
- Open ADUC (dsa.msc)
- Right-click your domain (e.g., corp.local) → New → Organizational Unit
- Create top-level OUs (uncheck protection for lab):
| OU Name | Purpose |
|---|---|
| IT | IT staff & servers |
| Finance | Accounting team |
| HR | Human Resources |
| Marketing | Sales & campaigns |
- Create sub-OUs (Right-click parent OU → New → OU):
IT → Systems Team
IT → Network Team
Finance → Accountants
HR → Recruiters
Marketing → Sales Team
Expected Result: 4 top-level + 6 sub-OUs. Refresh ADUC to verify structure.
STEP 2: CREATE SECURITY GROUPS
Groups assign permissions (e.g., AWS Console Access, File Share Read).
- Right-click IT → Systems Team → New → Group
- Configure groups (Global scope, Security type – most common):
Name: Windows-Admins | Scope: Global | Type: Security
Name: Network-Admins | Scope: Global | Type: Security
- Repeat in other OUs:
| OU | Group Name |
|---|---|
| Finance | Finance-Managers |
| HR | HR-Recruiters |
| Marketing | Sales-Team |
Pro Tip: Global groups for cross-forest access; nest in Domain Local for permissions.
STEP 3: CREATE & POPULATE USERS
Add 25 users simulating 2 locations (NY/Hospital-LA style).
- Right-click OU → New → User
- Example: IT → Systems Team:
- First: John | Last: Smith | Logon: jsmith
- Password: P@ssw0rd123 | Check: “Password never expires” (lab only)
- Finish → Right-click user → Properties → Member Of → Add → Windows-Admins
- Copy-Paste Users (create 5 per department):
IT-Systems: jsmith, mjohnson, rwilson, sgarcia, tlee
IT-Network: dkim, lmartin, pchen, kwalker, hnguyen
Finance: abrown, cwilson, ejones, fgreen, hwhite
HR: imorales, jrodriguez, klopez, mmendez, ngomez
Marketing: ohernandez, pperez, qramirez, rsanchez, ttorres
PowerShell Bulk Create (Run as Admin):
Import-Module ActiveDirectory
$Users = @(
@{Name='John Smith';Sam='jsmith';OU='OU=Systems Team,OU=IT,DC=corp,DC=local';Group='Windows-Admins'}
@{Name='Mary Johnson';Sam='mjohnson';OU='OU=Systems Team,OU=IT,DC=corp,DC=local';Group='Windows-Admins'}
# Add more...
)
foreach ($User in $Users) {
$Pass = ConvertTo-SecureString "P@ssw0rd123" -AsPlainText -Force
New-ADUser -Name $User.Name -SamAccountName $User.Sam -Path $User.OU -AccountPassword $Pass -Enabled $true
Add-ADGroupMember -Identity $User.Group -Members $User.Sam
}
Get-ADUser -Filter * | Export-Csv users.csv # Verify & Export [web:10][web:26]
Output: 25 enabled users in OUs, added to groups. Verify: Right-click group → Properties → Members.
STEP 4: SIMULATE ORG CHANGES & VERIFY
Test real-world scenarios.
- Move Users: Drag jsmith from IT-Systems to IT-Network (inheritance preserved).
- PowerShell Restructure:
# Move 10 users between OUs
Get-ADUser -Filter "Department -eq 'Sales'" | Move-ADObject -TargetPath "OU=Sales Team,OU=Marketing,DC=corp,DC=local"
# Export report
Get-ADUser -Filter * -Properties * | Export-Csv report.csv
- Verify:
dsquery user OU=IT,DC=corp,DC=local # List IT users
Get-ADGroupMember "Windows-Admins" # Group members [web:5]
✅ Success Check: 25 users, 8 groups, hierarchical OUs. Run
dsquery ou DC=corp,DC=local– no errors.
KEY TAKEAWAYS
- OU Hierarchy: Department → Team → Sub-team enables GPO/delegation
- Groups ≠ OUs: Groups for permissions; OUs for policy/organization
- PowerShell Scales: Bulk ops save hours in production
- Lab → Prod: Enable OU protection, enforce password changes
FAQ
Q: Users in wrong OU after move? A: GPO inheritance follows new OU. Re-apply policies via gpupdate /force.
Q: “Access Denied” creating OUs? A: Use Domain Admin or delegate: Right-click OU → Delegate Control.
Q: Bulk delete for cleanup? A: Remove-ADOrganizationalUnit -Recursive -Confirm:$false "OU=IT,DC=corp,DC=local".
NEXT STEPS
Practice daily: Day 1 recreate from memory; Day 3 mimic your company chart. Extend this lab with GPOs or join clients to domain.
Drop your lab results in comments! Share with #ADLab. Subscribe for Azure AD/Entra ID labs.